E-Commerce
E-commerce or electronic commerce refers to all transactions that occur on an electronic device between customers and businesses. It can be divided into consumer-to-consumer, business to consumer and business -to-business.
E-Commerce Apps
E-commerce applications are apps that allow consumers to choose the product they want purchase on the Internet. These applications are supported both by mobile phones and personal computers, and their functioning is quite similar to that of a retail website.
E-commerce Fraud
Sometimes, consumers don’t get the product that they order using an e-commerce application or website, which is referred to as e-commerce fraud. For instance, if a person orders an iPhone and gets an android phone instead, it would be an e-commerce fraud. It is a fairly common issue that most e-commerce users face.
E-Commerce Platform
An e-commerce platform is a type of software technology that provides merchants or e-commerce businesses an online store or shop from which customers can easily purchase what they want. An example of this is Shopify.
EID Services
eID services are used to identify users on a specific platform and are often used by key systems to ensure the security of the central building blocks of a Digital Single Market and cross-boarder electronic transactions. It allows owners of a given platform to identify the user who is visiting a specific platform.
Electronic Data Interchange
Electronic Data Interchange is an electronic communication method that provides standards for exchanging data. By adhering to the same standard, companies using EDI can transfer data from one branch to another across the world.
Email Address
An email address is a unique measure or identifier for a specific email account. It is used by people-- both to receive and send e-mail using the Internet. To send messages effectively, you need an address for both the recipient and the sender.
Email Fraud
Email fraud is a rather popular and inexpensive way to commit fraud. Fraudsters distribute fraudulent emails or messages to a variety of victims, generally with the goal of attaining their passwords, usernames, or other personal information, which they can then use to commit fraud schemes.
Email Spam
Email spam, also known as junk mail, is an unsolicited email that is sent to many people. Generally, there is no meaning to this mail and is generally meant to bring the receiver to a certain website.
Email Tumbling
Email Tumbling - What is It?
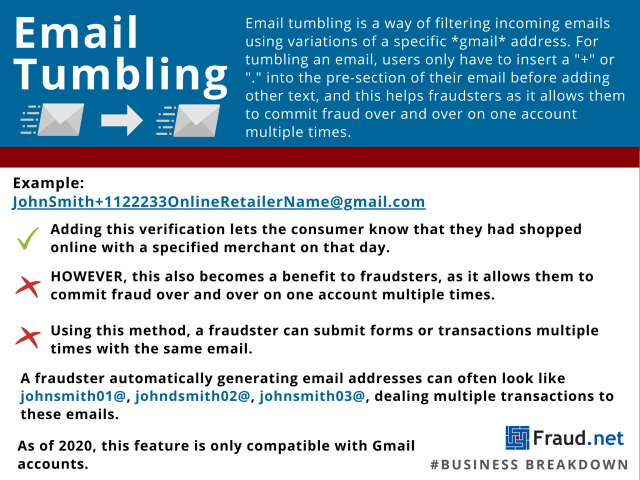
Email tumbling is a way of filtering incoming emails using variations of a specific gmail address. For tumbling an email, users only have to insert a "+" or "." into the pre-section of their email before adding other text. While this might be helpful to consumers in some regards, it could allow vehement abuse from fraudsters also. For example, a consumer can tag an email for a specified site as JohnSmith+1122233OnlineRetailerName@gmail.com, which would allow them to know that they had shopped online with a specified merchant on that day. However, this also becomes a benefit to fraudsters, as it allows them to commit fraud over and over on one account multiple times. Using this method, a fraudster can submit forms or transactions multiple times with the same email.
Email tumbling can also refer to the use of sequential email addresses when it comes to fraud. For example, organized fraud transactions can go through multiple emails with sequential numbering. A fraudster automatically generating email addresses can often look like johnsmith01@, johndsmith02@, johnsmith03@, dealing multiple transactions to these emails.
What are Some Solutions?
One way to prevent such scams from happening is identity and address verification. To prevent multiple transactions from occurring, Fraud.net incorporates dozens of data attributes on shipping and billing addresses, phone numbers and email addresses. IP address verification, as well as data mining. Preventing fraudsters from taking advantage of email tumbling can be automated into your business's fraud prevention services.
Email Verification
Email verification is a popular method of authentication that will ask a consumer to verify that it is really them trying to make a purchase by sending them an email with a link attached. Clicking on the link allows a business to see that the person making the purchase is someone who can access that email address.
Employment Scam
Employment scams refers to when advertising scammers create fake job listings in order to collect personal information of applicants, such as payment credentials and other types of information that can be used for blackmailing the applicants.
Emulator
An emulator is a special kind of robot that copies human activity when it comes to purchasing a service or product. Examples of emulators include targeted scripts which are aimed at buying a limited-quantity of items or at gaining an advantage in a time-limited sales event.
EMV
Europay Mastercard Visa or EMV is an international standard for debit and credit cards which are based on chip card technology. EMV cards are able to make in-person transactions safer than before, but the risk of card-not-present transactions has increased with it.
Encryption
A method of coding data, using an algorithm, to protect it from unauthorized access. There are many types of data encryption, which are the basis of network security. Encryption is the process of converting data into cipher text to prevent it from being understood by an unauthorized party. When e-commerce merchants need to securely transmit transaction data, including credit card information, they rely on encryption coding data so that only authorized parties can access it. Converting this regular data into ciphered (encrypted) data makes it difficult for an unauthorized third person to intercept the data and use it for illegal purposes. And even if the encrypted data is intercepted by a hacker, they’ll be unable to decode the information without the decryption key. The major data breaches of 2017 — including the exposure of the personal data of 143 million Americans — illustrate the importance of merchants encrypting customers’ sensitive information and protecting it from falling into fraudsters’ hands.
End-to-End Encryption
End-to-End Encryption refers to the protection of confidentiality and integrity which is not interrupted in terms of data by encoding them at the time of sending and decoding them at the end of the transaction. This method ensures that data is kept confidential no matter what.
Endpoint Authentication
Endpoint Authentication refers to a security system that aims to verify the identities of devices which are remotely connected along with their users like PDAs or personal digital assistant or a laptop before giving access to corporate network resources. It helps the user to know all the connected devices.
Endpoint Protection
Endpoint protection refers to a variety of solutions that are used to protect and detect a compromise of the last user's computer device linked to the mobile device and laptop, etc. Generally, endpoint protection solutions use one or more technique for protection.
EV SSL
The certification of EV SSL is actually the symbol of the highest level of trust for a virtual business. All modern browsers support a completely new technology, known as EV or Extended Validation which offers color-coded alerts which are used to inform about the website validity.
Exclusivity
Exclusivity refers to a contractual clause in which one party grants another party a right to use a specific business function. It means that the other party can now use the function as it likes.